Presented as a system capable of guaranteeing privacy, ease of use and security, the new European age verification app has already come under fire. What raises the doubts are not political criticisms or generic suspicions, but very harsh technical analyses, which speak of concrete vulnerabilities and, above all, of a deeper problem: the app would be able to certify that the person using it is “over 18”, but not that they are really the person to whom that credential was issued.
The case explodes after Ursula von der Leyen publicly promoted the app, claiming that it respects “the highest privacy standards”, that it works on any device and is completely open source. But a few hours later, security consultant Paul Moore showed how it was possible to bypass some of the app’s protections very quickly. According to the analysis later relaunched by the Signal Pirate website, it is not a single bug, but a series of flaws that call into question the overall reliability of the system.
Bypassing #EU #AgeVerification using their own infrastructure.
I’ve ported the Android app logic to a Chrome extension – stripping out the pesky step of handing over biometric data which they can leak… and pass verification instantly.
Step 1: Install the extension
Step 2:… https://t.co/9zSony8Em4 pic.twitter.com/a5oQnf0n2Y— Paul Moore – Security Consultant (@Paul_Reviews) April 16, 2026
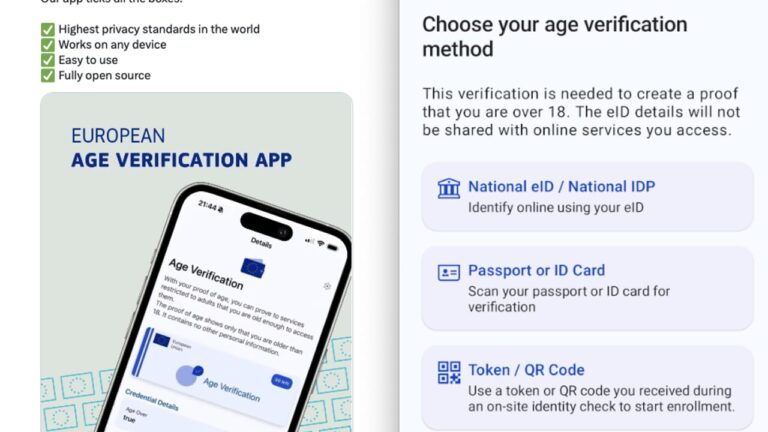
The expected operation, on paper, is simple. The user installs the app, sets a PIN and obtains a digital credential from a trusted authority that certifies only one piece of information: that he or she has exceeded the age of 18. When a site asks to verify your age, the app presents this signed credential, without providing your name, date of birth or other personal information. This is precisely the strong argument of the project: verifying age without identifying the person.
The problem, however, is that the fragility of the model lies precisely here. If the system only certifies that a valid credential with the word “over 18” exists, but fails to ensure that the person presenting it is the legitimate holder, then that proof risks becoming little more than a reusable token. The site receiving the verification checks the signature, but would not have enough tools to know who is really using that credential at that moment.
In detail, the analysis talks about eight confirmed vulnerabilities on the project’s official test environment. Among these, the possibility of resetting the PIN without invalidating the credentials already stored in the wallet; the possibility of resetting the counter that blocks attempts after too many errors; the use of protection mechanisms deemed weak; the absence of strong encryption of the local database that contains the credentials; and, in some test scenarios, the ability to extract and reuse the same credentials outside the official app.
An unsolvable problem?
According to the report, many of these flaws could theoretically be corrected with patches and refactors: greater database protection, tighter link between PIN and credential store, stronger user authentication, certificate pinning. But the real issue would be another, namely the basic architecture of the system. If the project wants to maintain a strong promise of privacy, avoiding tying a credential too closely to a personal identity or a specific device, then it becomes more difficult to completely prevent copies, replays or misuse. If, however, a stronger link is introduced between credential and person, the risks of tracking increase. In other words: privacy and anti-fraud, in this case, seem to come into tension.
This is the most delicate point that emerges from the work published by Signal Pirate: not only the presence of implementation bugs, but the suspicion that the political promise of the project is ahead of its technical maturity. The app is described as a solution ready for use on a large scale, but according to those who have analyzed it closely it still looks too much like a prototype exposed to weaknesses that, in an infrastructure intended for millions of citizens, should not exist.
The consequence is evident. If the European age verification system really wants to become a reliable standard, it will not be enough to reiterate that it is open source or that it minimizes shared data. It will be necessary to demonstrate, with independent verifications and substantial corrections, that that credential cannot be circumvented, copied or used by those who are not entitled to it. Because the risk, otherwise, is that Europe presents as a guarantee of security an instrument that today certifies only one fact – “of age yes or no” – without being able to guarantee who the person on the other side of the screen really is.